You’re trying to access geo-blocked content or hide your IP address. A free proxy seems like the perfect solution. No credit card, no commitment, just instant access.
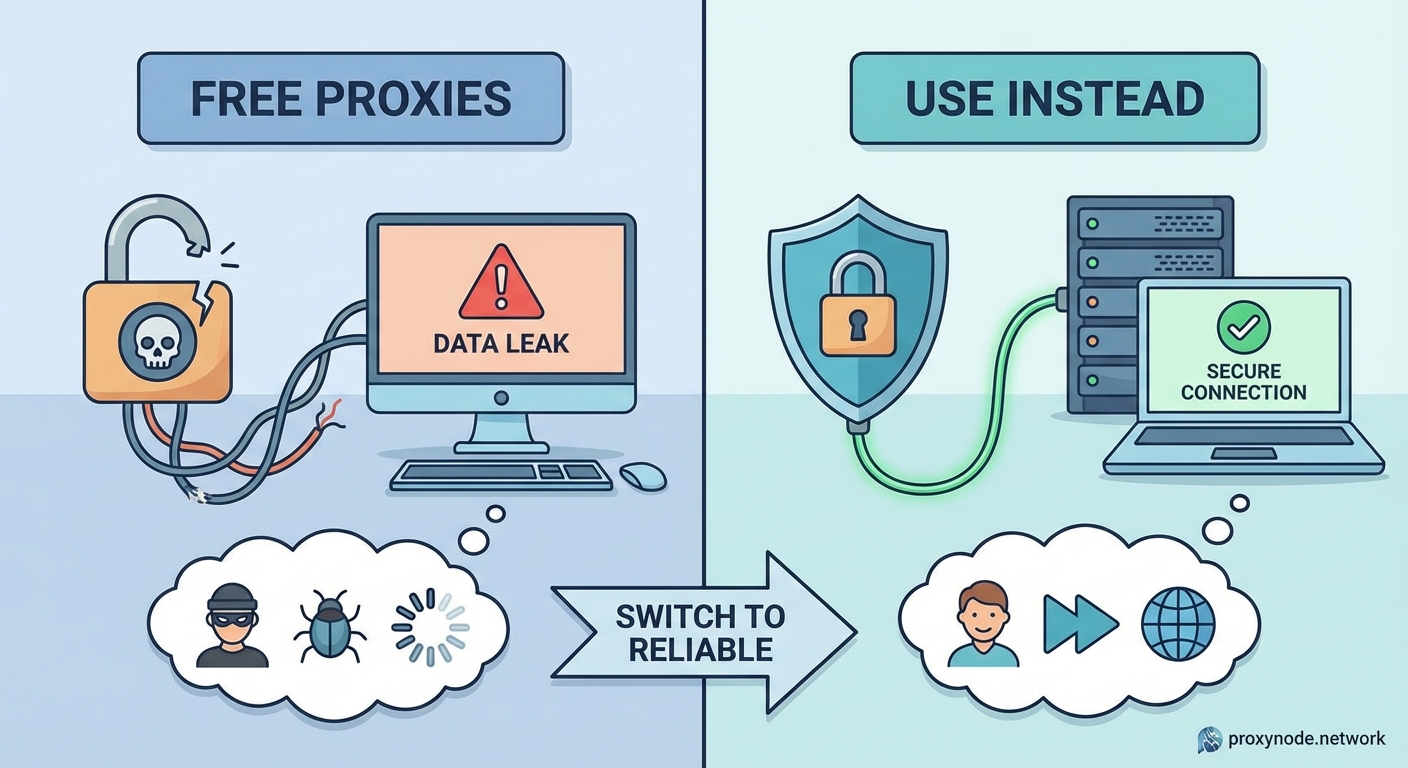
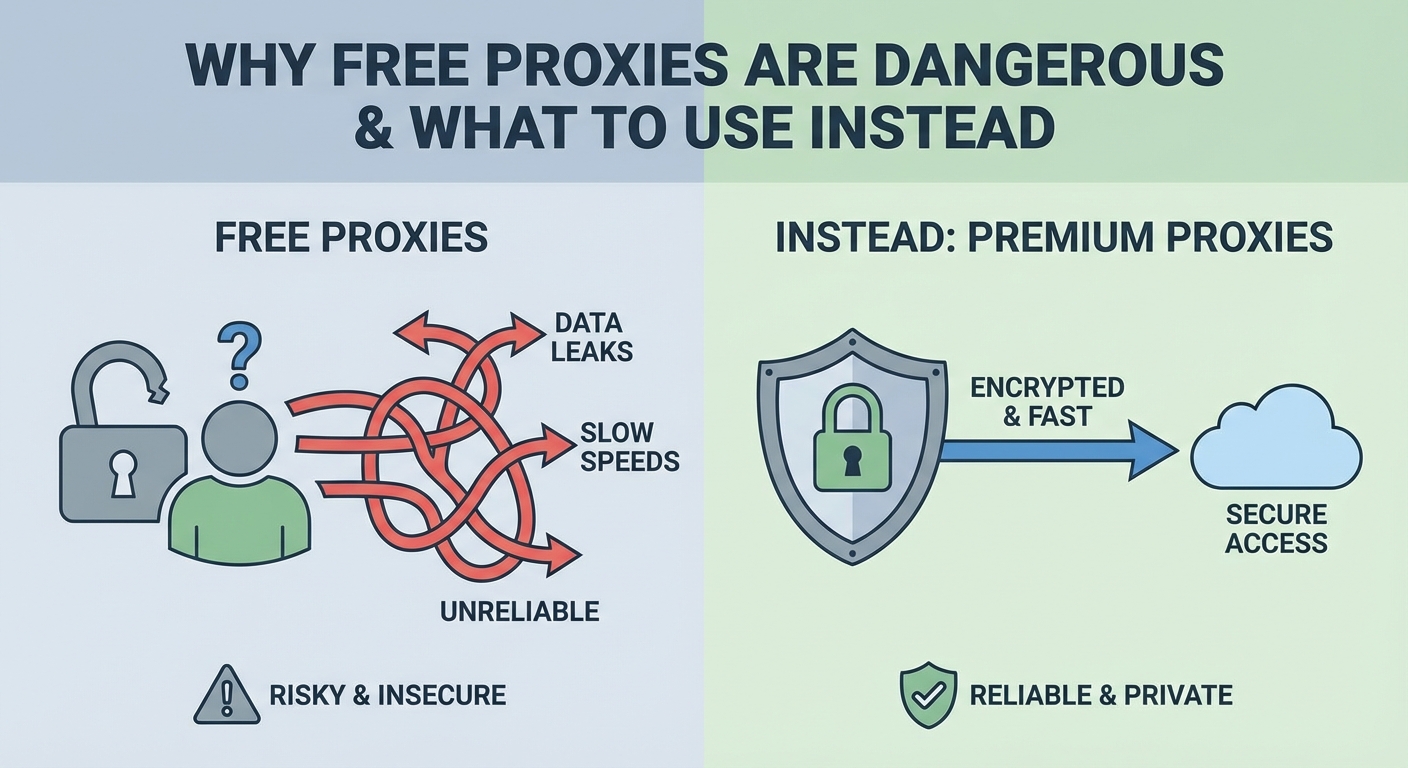
But here’s the problem: free proxies can expose you to serious risks that paid services don’t. From data theft to malware injection, these tools often do the opposite of protecting your privacy.
Free proxies typically log your browsing activity, inject ads or malware into your traffic, and may sell your data to third parties. Many operate with no accountability, leaving you vulnerable to identity theft, credential harvesting, and security breaches. Paid proxy services or VPNs with transparent privacy policies offer better protection and reliability for anyone serious about online privacy.
How free proxies actually make money
Nothing online is truly free. Someone always pays, and with free proxies, that someone is usually you.
Free proxy operators need to cover server costs and turn a profit. Since they’re not charging users directly, they monetize in other ways. The most common method is selling your browsing data to advertisers, data brokers, or worse.
Your browsing history reveals a lot about you. The sites you visit, the products you search for, your location patterns. All of this has value. Data brokers pay good money for detailed user profiles, and free proxy operators are happy to supply them.
Some free proxies inject ads into the websites you visit. You might notice extra banners, pop-ups, or redirects that weren’t there before. The proxy server modifies the HTML of web pages on the fly, inserting their own advertising code. This generates revenue but also slows down your connection and creates a terrible user experience.
The worst operators go even further. They inject malicious scripts that track your keystrokes, steal login credentials, or install malware on your device. These attacks are harder to detect because they happen at the network level, before the data even reaches your browser.
The logging problem nobody talks about

Most free proxy services claim they don’t log user activity. But there’s no way to verify these claims, and investigations have repeatedly shown they’re often false.
When you connect to a proxy, all your internet traffic flows through their servers. This gives the operator complete visibility into everything you do online. Every website you visit, every search query, every form you fill out. Without strong privacy policies and independent audits, you’re trusting a stranger with your entire digital life.
Many free proxies are operated by individuals or small groups with no legal accountability. They might be based in countries with weak privacy laws or no laws at all. If something goes wrong, you have zero recourse.
Even if the operator has good intentions, their infrastructure might not be secure. Free services typically run on cheap servers with minimal security measures. If their systems get breached, your data gets breached too. And you’ll probably never know it happened.
Paid services face market pressure to maintain trust. If they get caught logging data or suffering breaches, they lose customers and revenue. Free services face no such pressure. They can disappear overnight and reappear under a new name.
Security vulnerabilities you’re exposing yourself to
Free proxies often run outdated software with known security flaws. Maintaining secure infrastructure costs money, and free operators have little incentive to invest in it.
These vulnerabilities create opportunities for attackers. Someone monitoring the proxy server could intercept your unencrypted traffic, steal session cookies, or launch man-in-the-middle attacks. Your connection might feel private, but it’s actually less secure than using no proxy at all.
Many free proxies don’t support HTTPS properly. They might downgrade your secure connections to plain HTTP, stripping away encryption. This leaves your passwords, credit card numbers, and personal messages exposed to anyone watching the network.
Some proxies are actually honeypots set up by malicious actors specifically to harvest credentials and sensitive data. They advertise themselves as privacy tools while doing the exact opposite. Users trust them with their most sensitive information, never realizing they’re walking into a trap.
| Risk Type | How It Happens | Potential Impact |
|---|---|---|
| Data logging | Proxy operator records all traffic | Identity theft, blackmail, targeted attacks |
| Malware injection | Scripts added to web pages | Device infection, credential theft, ransomware |
| Credential harvesting | Capturing login details | Account takeover, financial fraud |
| Traffic manipulation | Modifying data in transit | Misinformation, phishing, financial loss |
| Unsecured connections | Weak or no encryption | Man-in-the-middle attacks, data interception |
Why business use is especially risky

If you’re using free proxies for work, you’re putting your entire company at risk. A single compromised connection can give attackers access to internal systems, customer data, and trade secrets.
Remote workers often use proxies to access company resources from restricted networks or locations. Using a free proxy for this purpose violates most corporate security policies, and for good reason. The proxy operator can see everything: internal documents, customer information, authentication tokens.
Small business owners sometimes use free proxies to research competitors, scrape data, or manage multiple accounts. This creates liability issues. If the proxy is used for illegal activity by other users, your business’s IP address might get associated with that activity. You could face legal consequences for something you didn’t do.
The reputational damage from a security breach can be devastating for small businesses. Customers expect you to protect their data. If they find out you were using sketchy free tools that compromised their information, they’ll take their business elsewhere.
The performance issues nobody mentions
Free proxies are notoriously slow and unreliable. They’re often overloaded with users, leading to terrible connection speeds and frequent timeouts.
Since free operators don’t invest in quality infrastructure, their servers might be located far from you geographically. This increases latency and makes everything feel sluggish. Streaming video becomes impossible, and even basic web browsing turns frustrating.
Many free proxies have bandwidth limits or throttling. They might work fine for the first few minutes, then slow to a crawl once you hit their cap. This makes them useless for any serious work.
Uptime is another major issue. Free proxies disappear without warning. The server might be online today and gone tomorrow. You can’t rely on them for anything important.
If you’re not paying for the product, you are the product. This old saying applies perfectly to free proxy services. Your data, your privacy, and your security are the currency these operators trade in. The small cost of a legitimate service is nothing compared to the potential cost of a data breach or identity theft.
What you should use instead
Reputable paid proxy services and VPNs offer the privacy protection you’re actually looking for. They have business models based on subscriptions, not data harvesting.
Look for services with clear privacy policies that explicitly state they don’t log user activity. The best ones undergo independent audits to verify their claims. This transparency matters.
A good VPN or proxy service should offer:
- Strong encryption protocols that protect your data in transit
- A strict no-logs policy verified by third-party audits
- Servers in multiple countries for flexibility and speed
- Responsive customer support when issues arise
- Transparent ownership and jurisdiction information
For business use, consider residential proxies from established providers. These cost more but offer legitimate IP addresses that won’t get flagged or blocked. They’re essential if you’re doing market research, competitor analysis, or managing multiple accounts professionally.
If budget is a concern, many reputable VPN providers offer affordable plans. You can often find deals for around five dollars per month. That small investment buys you real privacy protection, reliable performance, and legal accountability.
Spotting the warning signs
Not sure if a proxy service is trustworthy? Here are red flags to watch for:
- No clear information about who operates the service or where they’re based
- Claims of being “completely free forever” with no explanation of their business model
- Requests for unnecessary permissions or personal information
- Negative reviews mentioning data breaches, malware, or suspicious activity
- No HTTPS support or warnings about insecure connections
- Aggressive advertising or redirects to sketchy websites
- Promises that sound too good to be true
If you see multiple red flags, walk away. Your privacy and security are worth more than the convenience of a free tool.
Even services that seem legitimate might have problems. Before committing to any proxy or VPN, read independent reviews from security researchers and privacy advocates. Look for technical analyses, not just marketing claims.
Making the switch safely
If you’ve been using free proxies, here’s how to transition to a safer solution:
- Stop using the free proxy immediately and clear your browser cache and cookies
- Change passwords for any accounts you accessed through the free proxy, starting with the most sensitive ones
- Enable two-factor authentication on all important accounts to add an extra layer of security
- Monitor your financial accounts and credit reports for suspicious activity over the next few months
- Research and choose a reputable paid VPN or proxy service based on independent reviews and audits
- Configure your new service properly, ensuring encryption is enabled and DNS leaks are prevented
The transition might feel like an inconvenience, but it’s necessary. The longer you wait, the more exposure you risk.
Protecting your privacy moving forward
Privacy and security require ongoing attention. Even with a paid service, stay informed about potential vulnerabilities and best practices.
Keep your VPN or proxy software updated. Providers regularly release security patches and improvements. Running outdated versions leaves you exposed to known vulnerabilities.
Use strong, unique passwords for every account. A password manager makes this easier and more secure than trying to remember dozens of complex passwords.
Be skeptical of free tools in general. Whether it’s proxies, VPNs, or any other privacy service, free almost always means compromised in some way. The exceptions are rare and usually come from non-profit organizations with transparent funding models.
Educate yourself about online privacy threats. The landscape changes constantly. What’s secure today might not be tomorrow. Following security researchers and privacy advocates helps you stay ahead of emerging risks.
Your privacy deserves better

Free proxies create a false sense of security while actually increasing your risk. They’re built on business models that fundamentally conflict with user privacy.
The few dollars you save aren’t worth the potential consequences. Data breaches, identity theft, and malware infections cost far more than a VPN subscription, both financially and emotionally.
Choose tools that align with your privacy goals. Pay for services that treat your data with respect. Read privacy policies, check for independent audits, and hold providers accountable.
Your online privacy is worth protecting properly. Don’t trust it to free services with hidden agendas.
