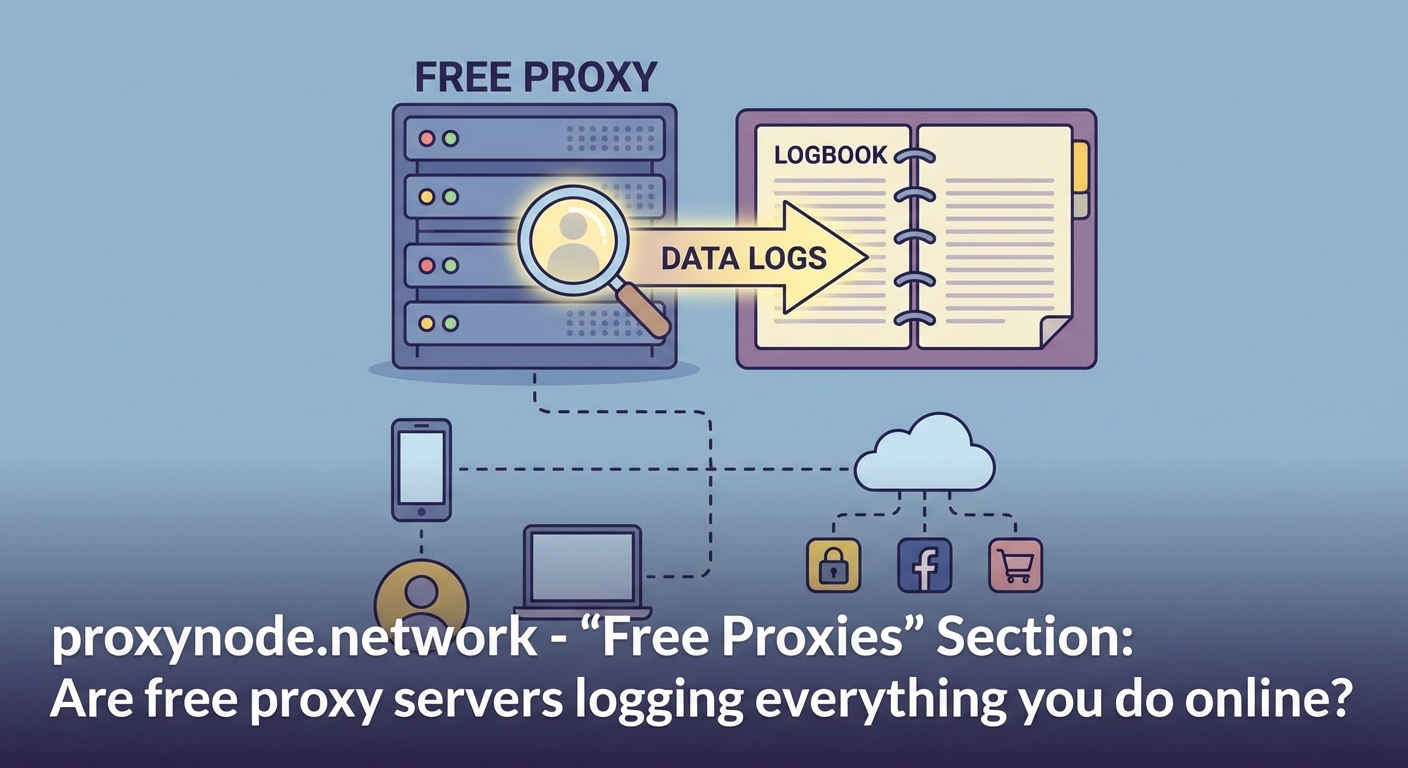
Free proxy servers show up everywhere online. They promise anonymous browsing, access to blocked content, and protection from prying eyes. All without costing a cent.
But there’s a problem. Most free proxies operate on a business model that contradicts the very privacy they claim to protect. Someone has to pay for servers, bandwidth, and maintenance. When you’re not the customer, you become the product.
Free proxy servers rarely offer genuine safety. Most lack encryption, log your browsing activity, inject advertisements, and sometimes distribute malware. The operators monetize your data by selling it to third parties or using your connection for questionable purposes. Paid proxy services and reputable VPNs provide better security through encryption, verified no-log policies, and professional infrastructure that doesn’t require exploiting users.
Understanding how free proxies actually work
A proxy server sits between your device and the internet. Your requests pass through this middleman before reaching their destination. The target website sees the proxy’s IP address instead of yours.
That’s the basic function. But the implementation matters enormously.
Free proxies typically run on minimal infrastructure. Operators cut costs wherever possible. This means outdated software, overcrowded servers, and zero investment in security features.
Many free proxy services operate in countries with loose data protection laws. Others hide their true location entirely. You have no way to verify who runs the service or what they do with your traffic.
The business model creates perverse incentives. Since users pay nothing, operators must find other revenue sources. Your browsing data becomes the product they sell.
The encryption problem that exposes everything

Most free proxies don’t encrypt your connection. Your data travels in plain text from your device to the proxy server.
Anyone monitoring the network can see everything. Your internet service provider, network administrators, or attackers on public WiFi can intercept your passwords, messages, and browsing history.
Some free proxies claim to use HTTPS. But this only encrypts the connection between the proxy and destination websites. The link between you and the proxy remains vulnerable unless the proxy itself uses HTTPS or SOCKS5 with encryption.
Even when encryption exists, you’re trusting the proxy operator completely. They can see everything passing through their servers. Without independent audits or transparency reports, you have no way to verify their claims about data handling.
Think about what passes through a proxy during normal browsing:
* Login credentials for email and social media
* Banking and payment information
* Private messages and personal photos
* Search history revealing sensitive interests
* Location data from various services
All of this becomes visible to whoever operates the proxy.
Data logging practices you need to know about
Free proxy operators commonly log extensive user data. This includes your real IP address, browsing history, timestamps, and sometimes even the full content of your requests.
The logs serve multiple purposes. Some operators sell anonymized browsing data to advertisers and data brokers. Others keep detailed records to comply with law enforcement requests or protect themselves from liability.
Many free proxy websites don’t publish privacy policies. Those that do often include vague language that permits unlimited data collection and sharing.
Consider this comparison of what different services typically log:
| Service Type | IP Address | Browsing History | Login Credentials | Duration |
|---|---|---|---|---|
| Free Proxy | Always | Usually | Often visible | Indefinite |
| Budget Proxy | Usually | Sometimes | Encrypted | Varies |
| Premium VPN | Minimal | No | Encrypted | 30 days max |
| Residential Proxy | Connection only | No | Encrypted | Session only |
The table shows clear patterns. Free services consistently log the most data for the longest periods.
Some operators use your connection for peer-to-peer proxy networks. Your device becomes an exit node for other users’ traffic. This means illegal activity could appear to originate from your IP address.
Malware and advertising injection risks
Free proxies frequently inject advertisements into the web pages you visit. Pop-ups, banners, and redirects appear even on sites that normally have no ads.
This isn’t just annoying. The injected ads often come from unvetted ad networks. They may contain malicious code that attempts to install malware on your device.
Security researchers have documented numerous cases of free proxies distributing:
* Cryptocurrency mining scripts that slow your device
* Spyware that records keystrokes and screenshots
* Ransomware that encrypts your files
* Browser hijackers that redirect searches
* Credential stealers targeting stored passwords
The infection process happens silently. You visit what appears to be a legitimate website through the proxy. Behind the scenes, the proxy modifies the page to include malicious scripts.
Your antivirus software might catch some threats. But many attacks use sophisticated techniques to avoid detection. The malware may remain dormant for weeks before activating.
Cookie theft and session hijacking
Cookies store authentication tokens that keep you logged into websites. When you browse through an unencrypted proxy, these cookies pass through the proxy server in plain text.
An attacker operating the proxy can copy your cookies. They can then use these stolen cookies to access your accounts without needing your password.
This technique, called session hijacking, works against any service you access through the proxy. Email, social media, banking, shopping accounts. All become vulnerable.
The attack leaves no obvious traces. You remain logged in and notice nothing wrong. Meanwhile, someone else accesses your account from a different location.
Two-factor authentication provides some protection. But many services only require 2FA during initial login, not for ongoing session access.
Performance issues that signal deeper problems

Free proxies typically offer terrible performance. Pages load slowly. Videos buffer constantly. Downloads fail partway through.
The poor performance stems from overcrowded servers. Free services attract massive user numbers. The operators run minimal infrastructure to keep costs down.
But slow speeds also indicate something more concerning. The proxy might be analyzing your traffic, injecting content, or routing your connection through multiple hops to obscure the operator’s location.
Some free proxies work perfectly for simple browsing but fail when you attempt secure connections. This happens because they can’t properly handle HTTPS traffic or deliberately block encrypted connections to maintain visibility into your data.
Frequent disconnections and IP address changes create another problem. Websites may flag your account for suspicious activity. You might face CAPTCHA challenges on every page or get temporarily banned.
When free proxies might be acceptable
Very limited scenarios exist where free proxies carry acceptable risk.
Testing basic geolocation features on your own website makes sense with a free proxy. You’re not transmitting sensitive data. You just need to verify how your site appears from different regions.
Accessing region-locked content on sites that don’t require login could work. But even then, you’re trusting the proxy operator not to inject malware.
Using a free proxy on a disposable device with no personal data reduces risk. Create a separate browser profile with no saved passwords or cookies. Never log into any accounts.
Academic research on proxy behavior might justify temporary use. But researchers should take extensive precautions and assume all traffic is monitored.
For anything involving personal information, financial data, or long-term use, free proxies create unacceptable risk.
Safer alternatives that actually protect privacy

Reputable paid proxy services offer genuine security. They charge subscription fees, eliminating the need to monetize your data.
Look for providers that offer:
- Verified no-logging policies audited by independent security firms
- Strong encryption for all connections (at minimum TLS 1.2)
- Transparent company information with verifiable physical locations
- Responsive customer support and clear terms of service
- Modern infrastructure with regularly updated software
Premium residential proxy networks provide even better anonymity. They route traffic through real residential IP addresses, making your requests indistinguishable from regular home internet users.
VPN services with proven track records offer comprehensive protection. They encrypt all traffic from your device, not just browser activity. Many VPNs maintain independently audited no-log policies.
Some VPN providers offer free tiers with limited bandwidth. These can work for occasional use. But read the privacy policy carefully. Even legitimate companies may log more data on free plans.
Building your own proxy on a cloud server gives maximum control. Services like DigitalOcean or Vultr let you deploy a personal proxy for a few dollars monthly. You control the software, logging, and security settings.
The golden rule: if you’re not paying for a privacy service with money, you’re paying with your data. Free tools might seem convenient, but they often create more vulnerabilities than they solve. Invest in verified services or accept that your activity isn’t truly private.
Red flags that identify dangerous proxies
Certain warning signs indicate a proxy service poses serious risk.
Avoid any proxy that:
* Requires installing browser extensions or desktop software
* Lacks HTTPS on its own website
* Shows no company information or contact details
* Displays excessive advertising on every page
* Requests unnecessary permissions or personal information
* Appears in lists of “free proxy sites” with dozens of alternatives
* Has no published privacy policy or terms of service
* Routes traffic through multiple unknown servers
* Blocks access to security-related websites
* Performs differently on encrypted versus unencrypted sites
Browser extensions deserve special caution. They request broad permissions to intercept all web traffic. Malicious extensions can steal passwords, inject code, and track everything you do online.
Check reviews from multiple sources. But remember that operators can post fake positive reviews. Look for detailed technical analysis from security researchers rather than generic user testimonials.
Making the right choice for your situation
Your specific needs determine the best approach.
For casual browsing without sensitive data, risks remain but consequences are limited. You might tolerate a free proxy for accessing region-locked content occasionally.
For anything involving login credentials, financial information, or private communications, free proxies are never safe. The potential for data theft, account compromise, and identity fraud far outweighs any cost savings.
Privacy-focused users should invest in verified services. A quality VPN costs less than a streaming subscription. Residential proxy services start around $50 monthly for legitimate providers.
Businesses and developers need professional proxy solutions. The risks of using free proxies include data breaches, compromised customer information, and legal liability.
Students and users with budget constraints should look for reputable free VPN tiers rather than free proxies. Services like ProtonVPN offer limited free plans with genuine encryption and verified no-logging.
Your privacy deserves better than free
Free proxy servers create a false sense of security. They promise privacy while systematically violating it.
The operators need revenue. They get it by logging your data, selling your browsing history, injecting advertisements, and sometimes distributing malware. Your real IP address, browsing habits, and personal information become commodities.
Encryption usually doesn’t exist. When it does, you’re trusting anonymous operators with complete visibility into your online activity.
Better options exist at reasonable prices. Paid proxies, residential networks, and verified VPNs provide real security. They encrypt your connection, maintain audited no-log policies, and operate transparent businesses.
Your online privacy matters. Protect it with services that align their business model with your interests, not against them.
